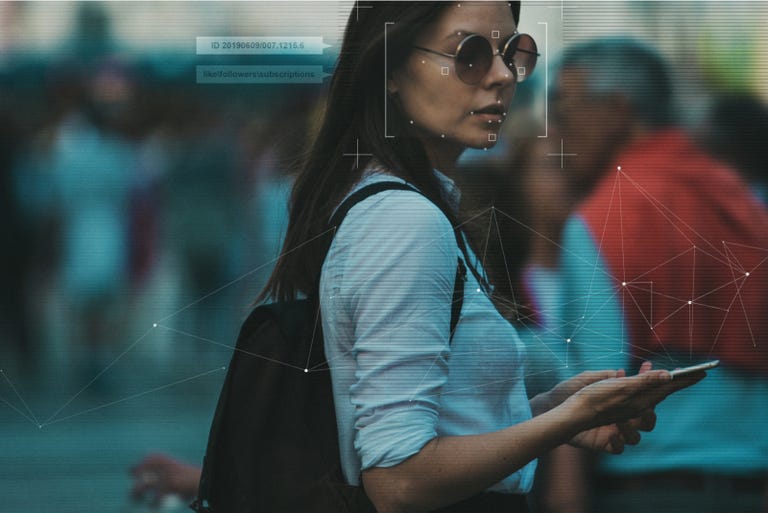
Surveillance apps are becoming more advanced. Here’s what to do if you think you’re being tracked.
must read
Read now

Image: iStock/Borislav
Our digital selves are now an established part of our identity. The emails we send, the conversations we have over social media — both private and public — as well as the photos we share, the videos we watch, the apps we download, and the websites we visit all contribute to our digital personas.
ZDNET recommends

The best VPN services
Every remote worker should consider a virtual private network to stay safe online.
There are ways to prevent a government agency, country, or cybercriminal from peeking into our digital lives, for example, by using virtual private networks (VPNs), end-to-end encryption, and browsers that do not track user activity.
However, governments and law enforcement agencies are now taking advantage of sophisticated spyware developed and offered commercially by companies, including NSO groups. It can be extremely difficult to detect or remove when implanted on a device.
This guide will run through different forms of malicious software on your iOS or Android handset, what the warning signs of infection are, and how to remove such pestilence from your mobile devices if it is possible to do so.
How to find and remove advanced spyware from your iOS, Android phone

What is spyware?
Trismegist san — Shutterstock
Nuisanceware is often bundled with legitimate apps. It interrupts your web browsing with pop-ups, changes your homepage settings by force, and may also gather your browsing data in order to sell it off to advertising agencies and networks. Although considered malvertising, nuisanceware is generally not dangerous or a threat to your core security.
You then have basic spyware. These generic forms of malware steal operating system and clipboard data and anything of potential value, such as cryptocurrency wallet data or account credentials. Spyware isn’t always targeted and may be used in general phishing attacks.
Advanced spyware, also known as stalkerware, is a step-up. Often unethical and sometimes dangerous, this malware is sometimes found on desktop systems, but it is now most commonly implanted on phone. Spyware and stalkerware may be used to monitor emails, SMS, and MMS sent and received; to intercept live calls for the purpose of eavesdropping across standard telephone lines or Voice over IP (VoIP) applications; to covertly record environmental noise or take photos; to track victims via GPS, or to hijack social media apps including Facebook and WhatsApp.
Stalkerware is often downloaded to spy on someone as an individual, such as in cases of domestic abuse.
You then have government-grade commercial spyware. Pegasus is the most well-known recent case, sold as a tool to governments for combating ‘terrorism’ and for law enforcement purposes — but ultimately was found on smartphones belonging to journalists, activists, political dissidents, and lawyers.
The warning signs of attacks

Phishing is one of the simplest cyber attacks for hackers to carry out – and one of the most effective.
Shutterstock
If you find yourself the recipient of odd or unusual social media messages or emails, this may be a warning sign of a spyware infection attempt. You should delete them without clicking on any links or downloading any files. The same goes for SMS content, too, which may contain links to lure you into unwittingly downloading malware.
To catch a victim unaware, these phishing messages will lure you into clicking a link or executing software that hosts a spyware or stalkerware payload. If the malware is being loaded remotely, user interaction is required, and so these messages might try to panic you — such as by demanding payment or pretending to be a failed delivery notice. Messages could potentially use spoofed addresses from a contact you trust, too.
When it comes to stalkerware, initial infection messages may be more personal and tailored to the victim.
Physical access or the accidental installation of spyware by the victim is necessary. However, it can take less than a minute to install some variants of spyware and stalkerware.
If your mobile goes missing and reappears with different settings or changes that you do not recognize — or it has been confiscated for a time — this may be an indicator of tampering.
How do I know when I’m being monitored?

Getty Images/iStockphoto
Surveillance software is becoming more sophisticated and can be difficult to detect. However, not all forms of spyware and stalkerware are invisible, and it is possible to find out if you are being monitored.
Android
A giveaway on an Android device is a setting that allows apps to be downloaded and installed outside of the official Google Play Store.
If enabled, this may indicate tampering and jailbreaking without consent. Not every form of spyware and stalkerware requires a jailbroken device, though.
This setting is found in most modern Android builds in Settings > Security > Allow unknown sources. (This varies depending on device and vendor.) You can also check Apps > Menu > Special Access > Install unknown apps to see if anything appears that you do not recognize, but there is no guarantee that spyware will show up on the list.
Some forms of spyware will also use generic names and icons to avoid detection. If a process or app comes up on the list you are not familiar with; a quick search online may help you find out whether or not it is legitimate.
iOS
iOS devices that aren’t jailbroken are generally harder to install with malware unless a zero-day exploit is used. However, the presence of an app called Cydia, which is a package manager that enables users to install software packages on a jailbroken device, may indicate tampering (unless you knowingly downloaded the software yourself).
Other signs
You may experience unexpected handset battery drain, overheating, and strange behavior from the device’s operating system or apps.
Surveillance without consent is unethical. In domestic situations, it causes a severe imbalance in power. If your sixth sense says something is wrong, listen to it. A physical object is not worth sacrificing your privacy and personal security.
Should your device become compromised, take back control of your right to privacy — whether or not this means replacing your handset entirely — but only if your physical safety isn’t being threatened. In those cases, you should contact the authorities and investigators rather than tamper with your handset.
How can I remove spyware from my device?
By design, spyware and stalkerware are hard to detect and can be just as hard to remove. It is not impossible in most cases, but it may take some drastic steps on your part. Sometimes the only option may be to abandon your device.
When removed, especially in the case of stalkerware, some operators will receive an alert warning them that the victim’s device has been cleaned up. Should the flow of your information suddenly stop, this is another clear sign that the malicious software has been removed.
Do not tamper with your device if you feel your physical safety may be in danger. Instead, reach out to the police and supporting agencies.
Now, here are some removal options:
- Run a malware scan: There are mobile antivirus solutions available that can detect and remove spyware. This is the easiest solution available, but it may not be effective in every case. Cybersecurity vendors, including Malwarebytes , Avast, and Bitdefender, all offer mobile spyware-scanning tools.
- Change your passwords: If you suspect account compromise, change the passwords of every important account you have. Many of us have one or two central ‘hub’ accounts, such as an email address linked to all of our other services. Remove access to any ‘hub’ services you use from a compromised device.
- Enable two-factor authentication (2FA): When account activity and logins require further consent from a mobile device, this can also help protect individual accounts. (However, spyware may intercept the codes sent during 2FA protocols.)
- Consider creating a new email address: Known only to you, the new email becomes tethered to your main accounts.
- Update your OS: It may seem obvious, but when an operating system releases a new version, which often comes with security patches and upgrades, this can — if you’re lucky — cause conflict and problems with spyware. Keep this updated.
- Protect your device physically: A PIN code, pattern, or enabling biometrics can protect your mobile device from future tampering.
- If all else fails, factory reset… or junk it: Performing a factory reset and clean install on the device you believe is compromised may help eradicate some forms of spyware and stalkerware. However, make sure you remember to back up important content first. On Android platforms, this is usually found under Settings > General Management > Reset > Factory Data Reset. On iOS, go to Settings > General > Reset.
Unfortunately, some stalkerware services may survive factory resets. So, failing all of that, consider restoring to factory levels and then throwing your device away.
An open source project developed by Amnesty International, MVT (Mobile Verification Toolkit) is a cyber forensics package able to scan for advanced spyware on mobile devices. However, this is most suited to investigators.
What about advanced spyware?
Government-grade spyware can be more difficult to detect. However, as noted in a guide on Pegasus published by Kaspersky, there are some actions you can take to mitigate the risk of being subject to such surveillance, based on current research and findings:
- Reboots: Rebooting your device daily to prevent persistence from taking hold. The majority of infections have appeared to be based on zero-day exploits with little persistence and so rebooting can hamper attackers.
- Disable iMessage and Facetime (iOS): As features enabled by default, iMessage and Facetime are attractive avenues for exploitation. A number of new Safari and iMessage exploits have been developed in recent years.
- Use an alternative browser other than Safari, default Chrome: Some exploits do not work well on alternatives such as Firefox Focus.
- Use a trusted, paid VPN service, and install an app that warns when your device has been jailbroken. Some AV apps will perform this check.
It is also recommended that individuals who suspect a Pegasus infection make use of a secondary device, preferably running GrapheneOS, for secure communication.
What are Google and Apple doing about this problem?
Google and Apple are generally quick to tackle malicious apps which manage to avoid the privacy and security protections imposed in their respective official app stores.
Several years ago, Google removed seven apps from the Play Store that were marketed as employee and child trackers. The tech giant took a dim view of their overreaching functions — including GPS device tracking, access to SMS messages, the theft of contact lists, and potentially the exposure of communication taking place in messaging applications. Google has also banned stalkerware ads. However, some apps still apparently slip through the net.
When it comes to Apple, the firm has cracked down on parental control apps, citing privacy-invading functions as the reason for removal. The company offers its own parental device control service called Screen Time for parents who want to limit their child’s device usage. Furthermore, the company does not allow sideloading, a practice Apple says stops mobile threats from proliferating in the iOS ecosystem.
Source: zdnet.com








